For a very long time, easily around late 2006 before booming tenfold in 2008 and occurring for years to come, there has been a part of Club Penguin you really don’t hear about much. In fact, you might not even know it exists. That world is hacking old and rare penguin accounts, then either making the account your own or selling it for profit. My longtime friend Pablo was one of the most active individuals in the Club Penguin account cracking community and has been kind enough to take the time to spill the beans on everything, revealing how it was done.

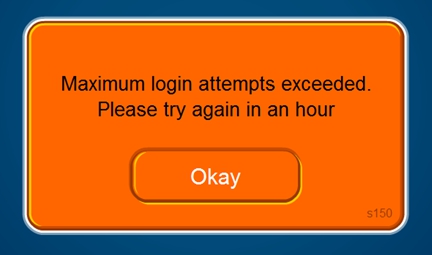
Back in this time period there weren’t any tools programmed for the task of cracking Club Penguin passwords, so instead everything had to be done manually. You had to come up with the username of a rare penguin you wanted to try guessing the password to, then come up with a few possible passwords to try. Common password guesses were the penguin’s username, “12345”, “password”, or “penguin”. Believe it or not, a lot of accounts actually had these very easy passwords. However, over time more potential passwords such as “soccer”, “football”, etc, were tried, which led the way to even more accounts. You had to be tactical, though, as after five incorrect login attempts you were temporarily unable to try any more login attempts for an hour.

This list of the 7,000 or so penguins was a godsend to those who wanted to guess passwords to rare penguins. After all, they now had a complete list of the oldest penguins to pick from and guess passwords to. These people trying to figure out passwords to accounts would spend hours each day going through penguins on the list and attempting to figure out what each password was. They would start with the basic username, 12345, or penguin passwords, before moving on to ones like clubpenguin, the names of sports, or some other common word such as computer.
There was a decent turnout of correctly guessed logins to penguins on the ID list from Microchip. It didn’t stop there, however. In July 2010 a user by the name of Jadencide posted his N-R-G Cracker v2 on the Hackforums website. This tools, when combined with Microchip123’s penguin ID list, was the ultimate penguin account cracker. N-R-G Cracker wasn’t focused on just Club Penguin, however. The ad supported program also had the ability to crack Pirates of the Caribbean Online and Toon Town accounts. The way it worked was simple. You fed the program a list of usernames to try, aka Microchip123’s list, and also a list of password to try on each penguin. It was able to bypass the five login attempts per hour restriction, making it an effective brute forcing program that could run all day, cycling through each username and trying every specified password on those accounts. There are large lists you can find online that contain every word in the dictionary. These are the types of password lists the people trying to crack accounts would use to figure out the login combinations to these old penguins.
The N-R-G cracker was not perfect. For starters, it was slow. It was only able to do one login per second. Sure, that’s 60 attempts a second, 3,600 attempts in an hour, or 86,4000 attempts in a day, but keeping in mind the fact that the Second Edition of the 20-volume Oxford English Dictionary contains entries for over 150,000 words, that’s about two days of password guessing every word in the dictionary for a single account if you were to guess each word as a single account’s password at the rate of one try per second.
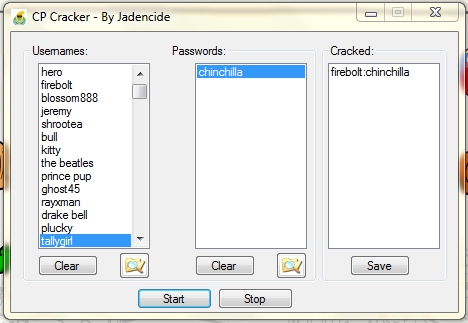
The N-R-G cracker continued to work and be used by players until January 2011, when Disney patched the exploit the cracking program was using. Jadencide had more tricks up his sleeve, however. He publicly released a new program, CP Cracker, a month later in February 2011. It worked the same as the N-R-G Cracker. You fed it a list of usernames and passwords and it would try all of the specified passwords on every listed penguin account. The program listed the usernames and passwords it was trying, plus there was a column listing any successfully cracked accounts. You could also save a list of the cracked passwords to a text file.
The program, while slow, did get the job done. The account crackers using this software didn’t care too much about the speed. As long as they successfully cracked some passwords to rare penguins, they were happy. The following video shows Jadencide’s CP Cracker running. It does a good job at showing you the speed of it.
The types of people using the CP Cracker program had different reasons for doing so. Some did it for the sake of selling the accounts to make some money. Others did it so they could have their own rare penguin accounts. Some were just simply curious or bored and only wanted to test it out and do nothing further with any gained account entry.
Jadencide was not the only one to make a Club Penguin cracking program. In late 2012 someone named Myles released his own. Unlike Jadencide’s programs which were coded in Visual Basic, Myles programmed his in Java. Not only that, but Myles didn’t distribute his for free like Jadencide’s. You had to pay Myles either $60 or 15,000 XATs (chat room currency) for it, a price that went up shortly after its initial launch. Copy protection was also put in the program, where unauthorised copies of it would not work. That means if someone purchased the cracker from Myles and sent the program to a friend to use too, it would not run on the friend’s computer because they did not pay for their own copy. However, in my tests, the copy protection scheme was poorly implemented and could very easily be circumvented, though it is not known if anyone other than myself realised this.
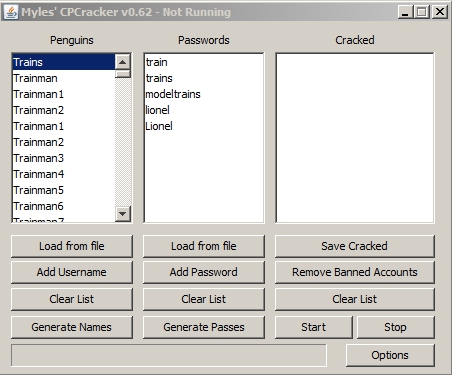
Compared to Jadencide’s cracker, the cracker from Myles was it far more complex in features and also a lot faster, meaning more accounts could be cracked in less time. Interface wise it was very similar to what Jadencide made. Penguins on the left, passwords in the middle, and successfully cracked penguins on the right.
The generate names and generate passwords features were something never before done. You could click the generate names button and enter a username prefix, e.g. “Trainman” and then it would ask for the number you want it to go up to, for example 1405. It would then add Trainman1, Trainman2, Trainman3, and so forth, all the way up to Trainman1405, to the username list for penguin accounts to try guessing passwords on. The generate passes feature worked the same way, but for passwords instead of usernames. At this point in time it wasn’t only about cracking rare penguin accounts, but rather about cracking any and all accounts people could get their hands on. The CPCracker program by Myles was also able to check if an account was banned. For example, if my penguin Trainman1405’s password was trainman but the account was banned forever, the CPCracker program would still list it as a cracked account because the login worked. The remove banned accounts button would check every cracked login to see if it was banned or not. This was done by using a flaw in Club Penguin’s Beta Team, where it would supply the cracked username and password to Club Penguin’s system and the Beta Team would return whether or not the account was banned. As for the options button in the program, it brought up settings to make it run faster, called turbo mode, and also whether or not to notify you when an account login was successfully found. The notification was a little popup in the corner of the screen. The Turbo mode feature was unstable, however. It would skip trying some of the logins that were specified to be tried. While it is unknown how long Myles’ cracker worked for, I do know that it worked until at least February 2013, but likely it lasted until later in 2013.
There are rumours of another Club Penguin cracker’s existence, one that still works, but because little information is known about it, I cannot say for sure. I was only told that it was coded in Python, is very slow, and is also kept private, meaning it’s not being shared or sold on the Club Penguin black market.
Aside from these cracker programs, there is another branch that is related to taking control over accounts that do not belong to you. This branch is security flaws on Club Penguin’s website that were abused to take control of penguin accounts. The first incident dates back to spring 2008, which became possible once Club Penguin released parent accounts in April of that year. Referred to as member hacking, you had to already know the username and password to an account, but from there you could take full control over the account by tricking Club Penguin into thinking you were the owner. Once their system thought you were the rightful owner of the account by having it under your own email, you could change the password to something more difficult and impossible for others guess.
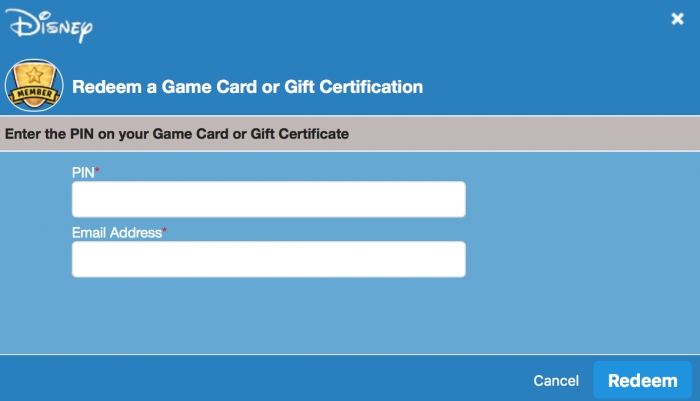
The email address you input could be any email; it did not have to be the one the penguin account was created under. The purpose of Club Penguin requiring an email address when redeeming membership is to send an invoice for it. Once the penguin became a member, you had to login to the parent account under that email address, go to the setting to add a new penguin to the parent account, then type in the penguin account’s login details. Because the email address the membership was redeemed under matched the parent account email, it automatically accepted it and the penguin was now under your own parent account, meaning you had complete control over it. Typically with the add penguin option in parent accounts, the email address the penguin is created under receives a confirmation email, but the member hacking bypassed this step since it thinks you’re the rightful owner of the account.
Member hacking was most popular until the launch of Jadencide’s first Club Penguin cracker, which was mentioned above. For two years people were guessing passwords manually, and if they got a good account login, they made it a member and got it added to their parent account so they could change the password and use it as their own.
The second security flaw Club Penguin had that let you take control over penguin accounts happened in July 2012. A big update was pushed out on their membership page, which consequently would show you the email address a penguin was registered under as long as you had the username and password to that account. Because it was now between six and seven years since the rare Club Penguin accounts being sought after were initially created, some of the email addresses they were created with no longer existed due to inactivity. This is where the security flaw in this comes in. Let’s say that back in October 2005 someone registered for Club Penguin with the username Penguin, the password Penguin, and the email address clubpenguinfan@yahoo.com. Fast forward to July 2012 when Club Penguin updated their membership page, all these years 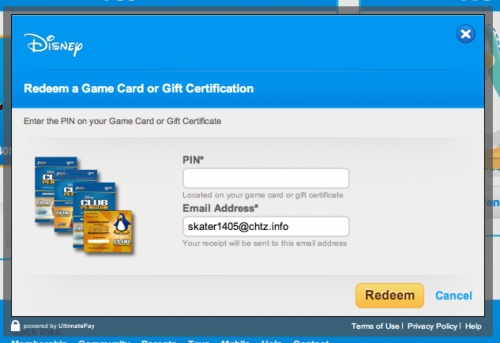
Back in 2012 was when Club Penguin released free 7 day memberships, which opened another line of abuse: many of these week long membership codes were gathered or generated, then used for member hacking. Because it was free, it saved having to pay $5.95 for each membership code for the member hack. In fact, Myles, the creator of the most advanced Club Penguin cracker, was the one who had made the 7 day membership code generator. While he didn’t share his tool with others, he generated tens of thousands of membership codes with it and would sell them in bulk for a low price.
There is another flaw, this one from 2013, where you could view the membership transaction details of any penguin, no login needed. Club Penguin’s parent account page had a URL that fetched the transaction history for the specified penguin ID. All you would have to do is take that URL and change the ID in it from your penguin’s ID to that of the penguin whose membership transactions you wanted to see, as it’s very easy to obtain a penguin’s ID number. It would then load their information rather than your own. With this info you could call Club Penguin, make up a bogus story about it being your penguin account, and because you have the membership transactions you shouldn’t be able to see, they think it’s the real owner of that account and thus would change the email from whatever legit address it was under to your own email, therefore giving you full control to the penguin account. Another method that was much more popular was emailing Club Penguin from a new email address you created and saying something along the lines of “Hi, my penguin name is _______ and I forgot my email and password. Can you please give me a hint of the email address so I can reset it?”. Club Penguin Support would then sometimes respond with a hint such as ac******@hotmail.com. You’d then have to try your best to correctly figure out what that email address was so the penguin could be yours. As far-fetched as it sounds, these methods have all been used successfully worked many times in the past. Eventually Club Penguin cracked down on this and you would be required to have to email them from the email address the account was originally created under, otherwise you were stuck. Of course, if you were able to recreate the email address or somehow figure out the password to the email account, this was no problem. Sometimes the penguin and the email address had the same password, so you could obtain an account that way.
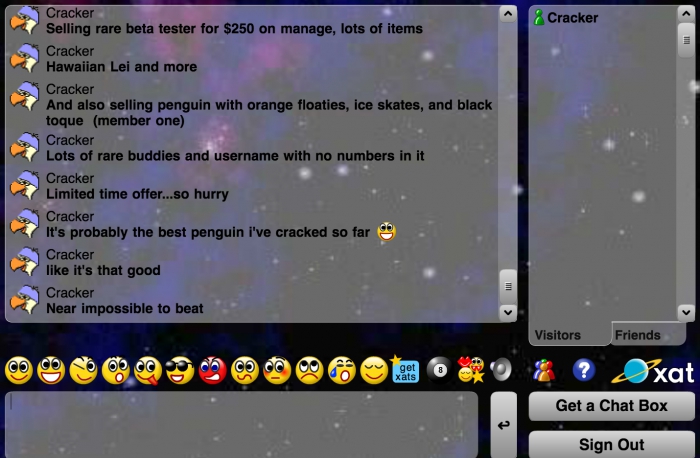
While some people would keep these cracked penguins for themselves, there was also an underground market for buying and selling them on XAT chat rooms. Before the Club Penguin community moved to Twitter, many players of the game would interact via XAT chat rooms. These rare accounts would be either traded or sold for money through PayPal or in exchange for premium XAT features such as “days” and “powers”, which enabled you to do special things in the chats. XATs could also be exchanged for real money. With XATs you could use exclusive smileys in chats, give your username name a special glow, and more. Some people would only have a few rare penguins to sell, while others were trying to sell literally 100 or more rare penguins at a single time. Back around 2012, beta tester penguins without the beta hat sold for about 15,000 XATs, which is equivalent $30. Beta tester accounts with the beta hat sold for 100,000 XATs, which is equivalent to $200. And yes, people did actually pay these astronomical prices just for pixels. In fact, some beta accounts would sell for $300, $500, and, I kid you not, even $1,000. It all depended on who was willing to pay top price for an account. The more rare the items the account had, the greater the value of it.
As time progressed, Microchip’s ID got shorter and shorter in length on accounts left to crack, as most accounts had been successfully cracked by players. A large majority of the beta tester accounts, those up to about ID 8,000 on the list, were cracked over time. No beta tester you see waddling around Club Penguin today is the legitimate original owner and there’s been no such thing for a long time. People became more and more clever with figuring out passwords, too. While a lot of Club Penguin fan sites nowadays use the WordPress platform, back in and around 2006 penguins would instead make a website with a now defunct website builder called Piczo. There was also some very old Club Penguin forums where some players would list their AIM (AOL Instant Messenger) screen names or email addresses on their profiles. These account crackers would pore over the Piczo websites and forum posts created by these old penguins in hopes of finding key information that would lead towards successfully guessing the password. They would search the pages on their Piczo websites for the smallest bit of information that could potentially be their password, for example the name of their pet. Google would also be searched by them in hopes of finding any other small piece of information that might help them figure out the password to an account. They were, more or less, desperate to find rare accounts, even if it meant spending hours trying to figure out the password to a single account. Old email addresses would sometimes be found on these websites too, which they would then try to remake just like with that membership page exposing emails flaw. My friend Pablo actually got a beta account for free simply by finding a comment from her on YouTube, messaging her and asking for the account, to which she replied and happily give it to him.

In fact, not even Club Penguin staff members themselves or their kids were immune to any of these cracks or hacks. At one point Dave Krysko’s penguin, Skidder, was member hacked after his password was cracked via one of the cracking programs. Ilsoap, Screenhog’s other penguin, was also hacked not only once, but twice. At one point Screenhog’s email address was even hacked into by Pablo’s friend who tricked the provider into letting him access the account. Pablo’s friend then temporarily took control of Screenhog’s account. Pablo’s friend had also looked through Screenhog’s emails to see what juicy information he could find, if anything. Pablo’s friend did later admit to Screenhog what he had done, to which Screenhog forgave him. Lastly, even the penguins owned by Billybob’s son (joeley) and daughter (Annie) have had their passwords cracked!
When Club Penguin launched their My Penguin mobile app in 2013, things were starting to slow down in the Club Penguin account cracking world. The game was becoming less and less popular, plus a flaw in the app paved the way for item adders, meaning the rare items on the cracked penguin accounts lost some of their value. Some of the people cracking accounts would use item adders to add items to the accounts they’ve cracked, i.e. if a penguin created in January 2006 never picked up the Hawaiian Lei item, they would use an item adder to add it to the account since it was from that time period and wouldn’t look suspicious to Club Penguin. Whereas, if a penguin created 2007 had the Beta Hat, that would be suspicious and result in a ban if Club Penguin found out. Item adders have been a constant game of cat and mouse for Club Penguin, they patch one and another appears.
Item adders was not the only flaw the mobile Club Penguin app paved the way for. With a packet sniffer of some sort, which is a program that searches your internet traffic and displays what is happening, people were able to sniff the packets of friends lists on mobile, and for reasons I do not know, the email addresses to those accounts would show up. Then you could give that email to Club Penguin to “prove” it’s you when they ask for the email it was originally created under, and from there you could get the email for the account changed to your own. Or, if it was possible, you could remake the inactive email account. This packet sniffing flaw sped up the process greatly for finding an email, as it saved you from having to search all over Google and old Club Penguin related websites trying to find the right piece of information needed. Combined with the aforementioned membership ID transaction flaw, anyone could have every piece of information that needs to be presented to Club Penguin support to make an account changed from its original email address to your own. While there is no real way to gauge exactly how many penguins have had their password successfully cracked, the number is definitely somewhere in the thousands range. I would personally estimate between 5,000 and 10,000, but really, I have no clue. The figure could very easily be double that, if not more.
If you are worried about the safety of your Club Penguin account, I wouldn’t that much. As long as you use a difficult password, one semi-lengthy and also with a mixture of uppercase and lowercase letters, plus a number or two and even a couple extra characters thrown in, it’d be near impossible to guess. Unless your account is deemed rare, nobody is going to bother trying to get into it. Besides, not only is Club Penguin past its days of giant popularity, but the account cracking scene is mostly, if not completely, dead now.
Does Club Penguin really delete inactive accounts? How long does it have to be inactive for it to be deleted?
Free accounts will be removed if you don’t log in for 1 year, and member accounts will be removed after 2 years.
http://help.disney.com/articles/en_GB/FAQ/Why-was-my-penguin-deleted?section=clubpenguin
Interesting, thank you for the information.
Also, haven’t heard from you in a while! I hope you return to blogging soon.
Quick question: how does Riyita have old SWFs of newspapers and catalogs?
He got them from Club Penguin.
Wow, internet is such a big and rare place, if all this is made for an account in a kids game, what could be done for more important topics? I just can’t imagine
Very interesting! I haven’t finished reading it, but I just want to say thanks for “cracking” this case wide open. Never thought I would see you post something on here again. :P
Cheers for the read Devin, excellent post.
This post brought me to tears, I’m not joking. The nostalgia is so strong… I remember the XAT communities of Cub Penguin and people selling/buying rare accounts (I remember I sold 4 or 5 rare accounts on Ebay in 2010/2011, you could make good money there). I remember the cracker program and the membership glitch that you could use to get control over an account (I think I did it twice with two 2006 accounts, I’m not proud of it though). I remember the glitch of Club Penguin’s app which you could use to add any item you wanted to your account (although I hate that one, it basically destroyed the meaning of rare items).
Do you remember when people could hack rare items using the coin codes from CP toys? If I recall correctly it started in 2009. I remember that very, very few people knew how to do this in the first years, I had to pay a good amount ($40) to a guy that added ~5 old items into my account. But then in 2012/2013 you could actually find the full tutorial online. It became a mess.
I’ve never met Microchip123 but I remember people used to worship him (especially in the Brazilian Club Penguin community, which was a huge one) for creating Penguin Storm. This program deluded me for many months to be honest, I remember you could become any celebrity (Rockhopper, Gary etc) you wanted but other people couldn’t see you dressed differently. I was so frustated that no one was giving me attention.
Well writen, Trainman! Thank you for this. It’s good to remember these things.
Btw sorry for my English. I’m not a native speaker.
I am hoping My Penguin does not get deleted as I might be gone for two years. I may have to tell my siblings to use it only every couple of months
They get deleted after one year? So that’s why I couldn’t log in with one of my old accounts. My siblings and relatives accounts must’ve been deleted too. There goes my memories.
Wow I never knew that account hacking and selling business was so popular and vast
Xat gaves me many memories
Interesting.
pls post ur password and username
for club penguin